Wapiti is an advanced automated command line vulnerability scanner. It helps penetration testers and bug bounty hunters to scan web based application to make it secure or search for loopholes. It is free and open source and has had some recent edits and updates. It comes with Kali Linux.
Wapiti Key Features
Wapiti can detect lots of vulnerabilities, so we don't need to manually visit every pages of an web application to find vulnerabilities. Wapiti can find following vulnerabilities:
- File disclosure (Local and remote include/require, fopen, readfile...)
- Database Injection (PHP/JSP/ASP SQL Injections and XPath Injections)
- XSS (Cross Site Scripting) injection (reflected and permanent)
- Command Execution detection (eval(), system(), passtru()...)
- CRLF Injection (HTTP Response Splitting, session fixation...)
- XXE (XML External Entity) injection
- SSRF (Server Side Request Forgery)
- Use of know potentially dangerous files (by using the Nikto database)
- Weak .htaccess configurations that can be bypassed
- Presence of backup files giving sensitive information (source code disclosure)
- Shellshock (aka Bash bug)
- Open Redirects
- Uncommon HTTP methods that can be allowed (PUT)
Installing and Using Wapiti on Kali Linux
Wapiti latest version (3.0.3 now) comes pre-installed with Kali Linux, if some Kali Linux lighter version doesn't have it installed then we can install it by simply using following command:
After installing this we can check the help section of this tool by applying following command:
The following screenshot shows the output of the applied help command:
Now we can run this tool against a website by using following command:
Then it will scan the website (https://target.site/ is just an example) for URL's. After the scanning process is done wapiti will run various modules for finding the vulnerabilities. We can see it on the following screenshot:
 |
| We run it on mutillidae web application on localhost |
Wapiti crawls all the pages and runs its modules on all the pages so it might be time consuming. On our this localhost machine it took more than 18 minutes to complete the scan and running the all modules. On a real website it might take hours.
If the website of web application have too many pages then it might take a very long time. Fortunately we can skip the modules. Suppose we know that our target website have not any blindsql vulnerability then we can skip this module. When the module blindsql is working we need to to press CTRL+C.
Then it will prompt with some options as the following screenshot:
Here if we press 'r' & Enter, then it will stop everything and generate the report. If we want to skip the running module then we just need to press 'n' and Enter, then wapiti will skip the module and run the next module.
Even we can continue the current attack using 'c', and quit without generating report by pressing 'q'.
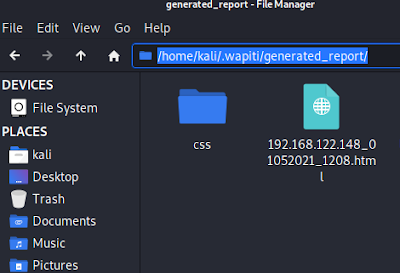
After the scan is complete we can see a HTML report is crated on our /home/kali/.wapiti/generated_report directory.
We can navigate to the directory from file manager (on in terminal using cd command):
Now we can open this on browser to see the full report. As we did in the following screenshot:
We can click on the found vulnerabilities to get additional information on this. Here is an closer look of XSS vulnerability on this Wapiti report.
This is how Wapiti works. It's very useful for cybersecurity researchers and bug bounty hunters.
There are lots of options in this tool we just checked the basics on our above section.
Wapiti can pause the scan and resume it later (It's very useful because sometimes it took whole day or more than it).
We can save our Wapiti report HTML file on a required directory by using following command:
Please don't forget to add a '/' after the target site (it requires the full address like https://mytarget.com/ not like mytarget.com ), otherwise Wapiti will not think the address is complete.
We can check the help section of this tool for more information. Carefully check the help section and tell us,
"What command we need to use if we just use the blindsql module on a website called https://target.com/ ?"
Got the answer? Please comment in the comment section. Question and answer will improve our learning.
For any problem or help we are always there. Please describe the full problem we always happy to help. We read each and every comment and, We always answer.
We are available on Twitter and GitHub, we share article updates there make sure to follow there to get updated. Also subscribe our E-mail subscription to get notification about new articles directly on e-mail.